PENTEST
- tools - huge list of pentest tookit
- vulnerability analysis by port / concrete protocols / 0daysecurity pentest by ports
- admin marks - my personal cheatsheet for little managment
injection attacks
Unproperly sanitized input results in ability for attacker to get out from data context into command context. It results in injection attacks: SQL, XML/XXE, HTML/XSS, JS, CSS, XPath, …
Correct processing of user-input:
- user-input checks must be done on server-side
- Validation: no blacklists, “accept known good” (in particular cases: type conversions (to numbers, dates))
-
technology specified (e.g. precompiled expressions)
- work with user’s files - harmful (use separate environment, disable execution, etc.)
- serialization/deserialization user’s input - harmful
- how to enable macros functionality? - very accurate filtration, anyway no reliability
network security
There is a lot of information channels ourdays: usb, ethernet, wifi, gsm, NFC, RFID, etc.
-
RCE (Remote Code Execution) - ability to execute code (any language: bash, PS, python, php, …) remotely.
OS-commanding - an attack technique used for unauthorized execution of operating system commands (e.g. bash RCE). - cryptography
- personal security - personal security: encryption, anonymity, fingerprinting, …
- random notes (phpinfo LFI -> RCE)
- default-passwords.json
How you can use this resource: sometimes you will find explanations or theory other times just use text search.
Other’s awesome cheatsheets
- bitvijays.github.io
- PayloadsAllTheThings (by swisskyrepo) - a list of useful payloads and bypasses for Web Application Security
- pentest-wiki (by nixawk)
- anhtai.me - pentesting-cheatsheet
- attackerkb.com
- python pentest tools
Analytics:
- ddosmon.net - DDoS
- Информационная безопасность банковских безналичных платежей. Часть 5. 100+ тематических ссылок про взломы банков
- Alexa top 500 sites on the web, Alexa top 1M sites on the web (zip)
- protect.me - security value from the point of customers
protect.me (pwc) (RU) - оценка важности безопасности с точки зрения конечного пользователя
Links intresting for normal users
- virustotal.com
nodistribute.com - online virus scanner without result distribution (it that true ??)
www.reverse.it
www.hybrid-analysis.com - huntingmalware - looks like virustotal analogue for linux executables (?)
- Honeypot Or Not?
- online tools for checking malicious signs - list of free online tools for looking up potentially malicious websites
- nomoreransom - detects type of ransomware (by email, BTC, url, …) and offer decryption tools for about 80 different encryption ransomware (“any reliable antivirus solution can do this for you”)
- сheck IMEI
- ZeuS Tracker - fake urls tracker
- OpenDirs: rghost.ru / danwin1210.me/upload.php / www.2shared.com / ddwa.top /
- Internet security thread reports (by symantec)
- Security trends & vulnerabilities review (Web applications) (by PositiveTechnologies) (2016)
- Security trends & vulnerabilities review (Industrial control systems) (by PositiveTechnologies) (2016)
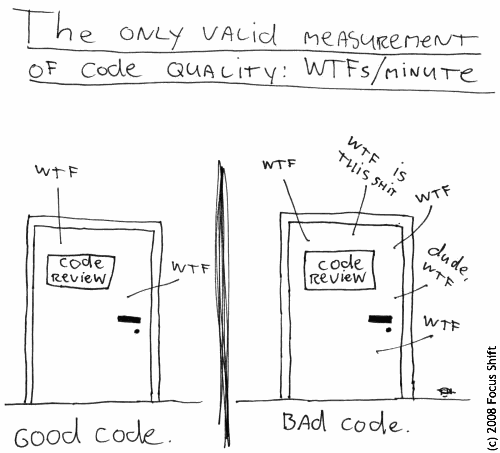
The only valid measurement of code quality: WTFs/minute
- CADT - the new programming paradigm
- https://xkcd.ru - comics
- SNMP - Security is Not My Problem